What is PAM
What are Privileged accounts?
Privileged credentials are those of an administrator who can make significant changes to cloud accounts, network systems, and other parts of a business’s technology infrastructure. This means that an admin can add and remove users, change security settings, and even execute automation scripts.
Why PAM?
PAM is a common practice for business owners and managers to not be aware of who has privileged access to their systems. This is because privileged accounts are often not tracked or monitored closely. Thus, making it an easily exploitable point to get into organisation’s systems by hackers. Often, when safeguarding an organisation’s environment against potential threats, one of the challenges is the oversight of certain privileged accounts, which can be exploited by attackers to gain unauthorised access to the organisation’s systems.
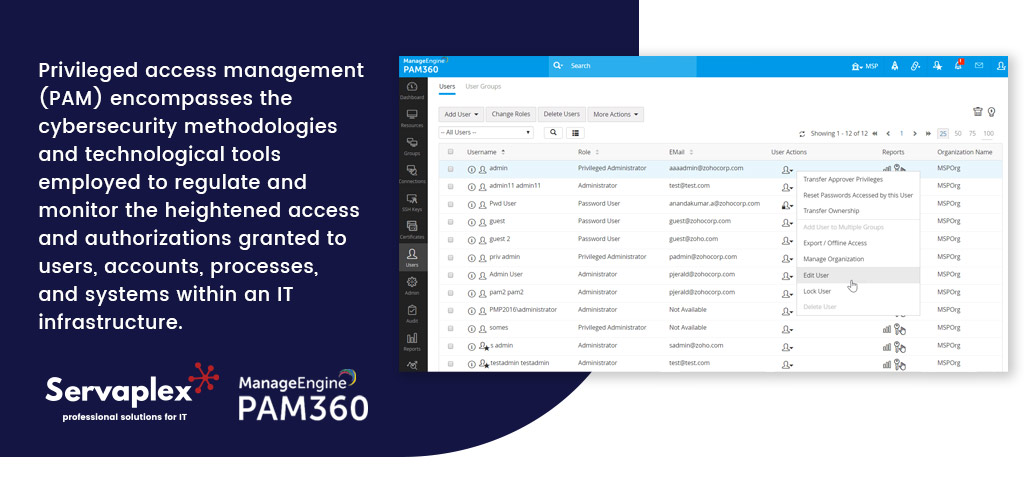
Privileged access management (PAM) encompasses the cybersecurity methodologies and technological tools employed to regulate and monitor the heightened access and authorisations granted to users, accounts, processes, and systems within an IT infrastructure. Through the appropriate calibration of privileged access controls, PAM aids organisations in reducing their susceptibility to security breaches and in minimising the potential impact of external attacks, as well as internal misconduct or carelessness.
PAM VS IAM
The area of privilege management is encompassed by the broader field of identity and access management (IAM) and identity security. When combined, PAM and IAM contribute to offering detailed control, visibility, and auditability over all credentials, privileges, and access.
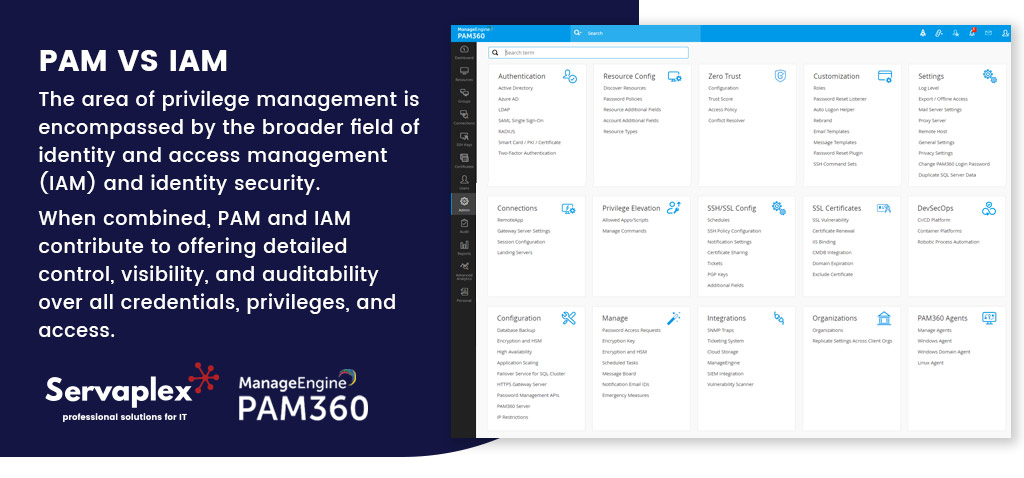
IAM controls are responsible for authenticating identities to ensure that the appropriate user has the correct access at the appropriate time. In contrast, PAM offers enhanced visibility, control, and auditing over privileged identities and session activities. PAM is considered essential for identity security, as it plays a central role in safeguarding enterprise assets and users in a perimeter less, work-from-anywhere (WFA) environment, according to analysts and IT leaders.
Major Features of PAM360?
1. Privilege elevation and delegation management (PEDM): Prevent security risks posed by standing privileges by implementing just-in-time controls for domain accounts, granting elevated privileges only when necessary and revoking permissions after a defined period. Additionally, enhances security by resetting passwords regularly.
2. Utilise Privileged User Behaviour Analytics (PUBA): Detect potentially malicious user behaviour by identifying unusual patterns and making informed security decisions with the assistance of AI and ML-powered anomaly detection capabilities.
3. PAM Auditing: Ensure audit and compliance by recording all events related to privileged account activities through precise auditing. Stay continuously prepared for compliance through the use of built-in reports.
4. DevOps Protection: Integrate password security seamlessly into the DevOps pipeline to safeguard your integration and delivery platforms from credential-based attacks, ensuring robust protection for your DevOps environment.
5. Application credential security: Securing application credentials entails deploying secure APIs for seamless communication between applications, eliminating the need for hard-coded credentials. This approach mitigates the risk of exploitation by malicious actors utilising server backdoors.
Why Should Companies Use PAM 360?
Privileged access misuse poses a significant security threat for enterprises, particularly in decentralised setups. In the initial two months of 2022, India’s CERT-In reported over 2000 cybersecurity incidents. This underscores the importance for enterprises to leverage solutions like ManageEngine PAM360
- Manage all privileged accounts collectively: Because privileged accounts have special permissions, they are essential for system administration. If they are handled improperly, there might be serious repercussions, such as system interruptions and data breaches. To reduce the dangers connected to these accounts, strong authentication, frequent monitoring, and strict access limits are necessary. To strengthen overall cybersecurity and stop unwanted access or abuse, proactive measures like audits and multifactor authentication are essential.
- Internal and externalattacks protection: Due to the expertise often associated with privileged users and the increasing occurrence of insider attacks worldwide, it is imperative to oversee and control privileged activities. This proactive approach is vital not just for preventing violations but also for thwarting external threats attempting to gain critical permissions.
- Action Traceability: Due to their access to vital corporate information and systems, privileged users are greatly relied upon by organisations. Unchecked activity by these people, however, presents serious security threats due to malevolent intent, honest errors, or compromised credentials used by cybercriminals.
ManageEngine PAM360, which provides thorough user activity tracing, may be used by businesses to remedy issue. PAM360 gives you accurate information on the operations carried out by administrative accounts, including dates and accountable parties. This information becomes essential for identifying breaches, data loss, and other problems as it clarifies the root causes and makes it easier to implement efficient countermeasures.

ManageEngine PAM360 Deployments
ManageEngine PAM360 deployments provide unmatched ease of use by relieving IT teams of the administrative strain related to privileged access control. For system administrators, the system manages passwords, access, and sessions on its own, guaranteeing effective and safe operations.
If you have an IT Problem then we’ve got the IT Solution, call us on +353-1-2304242 or contact us online for more info!




