Free Online Training, Workshops & Masterclasses
We’re happy to present free online training, workshops, and masterclasses to improve your knowledge.
If you can’t make it to a particular session, go ahead and register anyway as every session is recorded and you can watch at a time that’s convenient for you.
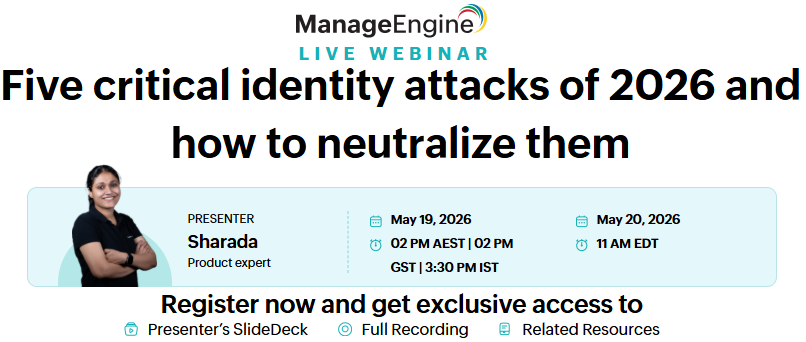
Five critical identity attacks of 2026 and how to neutralize them
May 19, 2026 02PM AEST | 02PM GST | 3:30PM IST
The identity threat landscape is evolving rapidly. Are you ready to protect your organization against the attacks of tomorrow? Join our exclusive webinar to uncover the most critical identity attacks of 2026 and learn how ADSelfService Plus helps neutralize them.
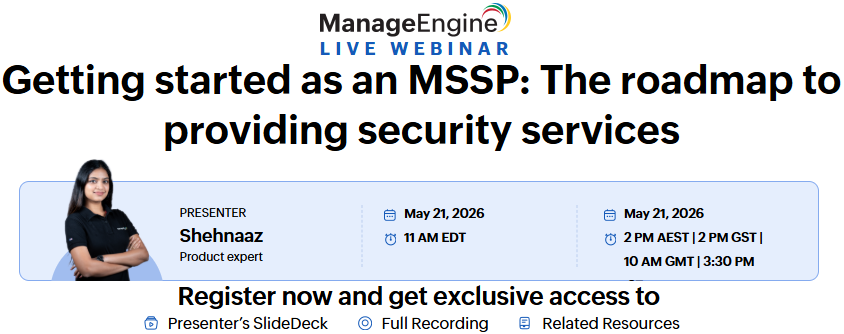
Getting started as an MSSP: The roadmap to providing security services
May 21, 2026 11AM EDT
Starting and scaling a Managed Security Service Provider (MSSP) practice requires the right strategy, tools, and operational framework. This webinar will help you understand the essential steps to build security service offerings, manage clients effectively, and deliver reliable protection in a competitive market.
Getting started as an MSSP: The roadmap to providing security services
May 21, 2026 11AM EDT
- What’s changing with SolarWinds pricing and licensing: A quick look at the shift to subscription models and multi-year commitments, and how it may affect your IT security and monitoring budgets.
- The hidden costs many teams miss during renewals: Understand the operational overhead that often comes with maintaining legacy monitoring and security tools in growing IT environments.
- What modern security teams expect today: Key capabilities teams look for today, from unified log visibility across IT environments to easier compliance reporting.
- How organizations are moving to more cost-efficient SIEM platforms:See how teams are improving security monitoring while keeping costs predictable.
- A closer look at ManageEngine as a SolarWinds alternative: See how ManageEngine helps teams centralize log management, strengthen SIEM capabilities, and simplify compliance across their IT environment.
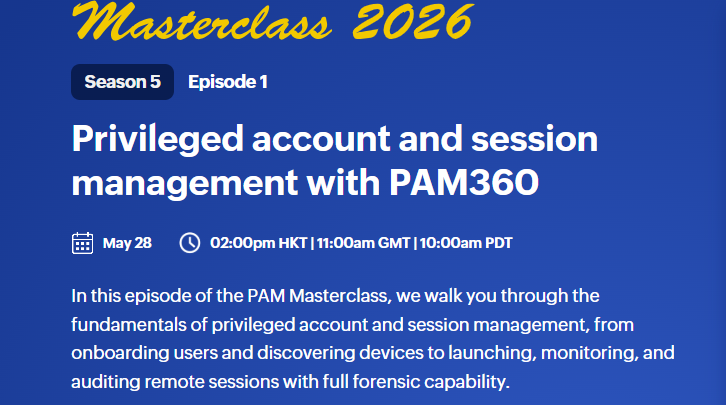
PAM360 Masterclass Episode 1: Privileged account and session management with PAM360
May 28, 2026 11AM GMT
In this episode of the PAM Masterclass, we walk you through the fundamentals of privileged account and session management, from onboarding users and discovering devices to launching, monitoring, and auditing remote sessions with full forensic capability.
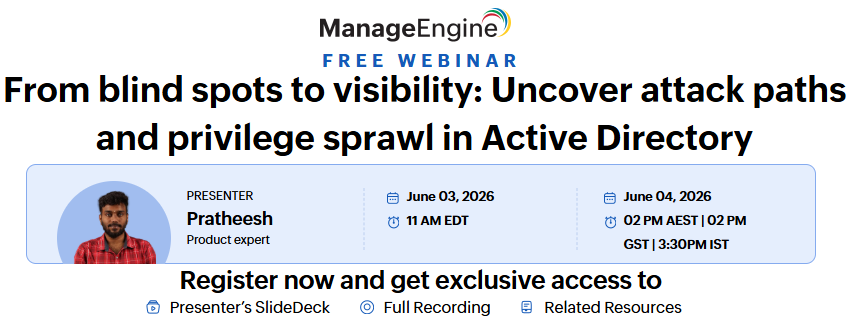
From blind spots to visibility: Uncover attack paths and privilege sprawl in Active Directory
June 03, 2026 11AM EDT
Hidden privileges and complex permission chains create security gaps in Active Directory. Most organizations don’t know how nested group memberships and inherited permissions create attack paths until it’s too late. Excessive access or a single misconfigured permission can give attackers the keys to your domain.
Join us to learn how to gain visibility into your Active Directory environment and eliminate privilege sprawl. You’ll see how to identify attack paths before attackers do, understand how permissions flow through your environment, and take action to reduce your risk exposure.
Maximize your OpManager investment with
powerful add-ons
June 11, 2026 6AM GMT and 11AM EDT
Your network may be monitored for availability and performance—but is that truly enough? Device uptime alone only tells part of the story. Beneath the surface, critical gaps often go unnoticed.
Untracked config changes break services. Silent firewall misconfigurations expose you. Hidden traffic patterns escalate into incidents. And application blind spots turn user frustration into your team’s emergency.
Join us to discover how your OpManager, with the right add-ons, goes far beyond device monitoring — giving you configuration tracking, traffic analytics, firewall optimization, security analytics, and application performance monitoring.
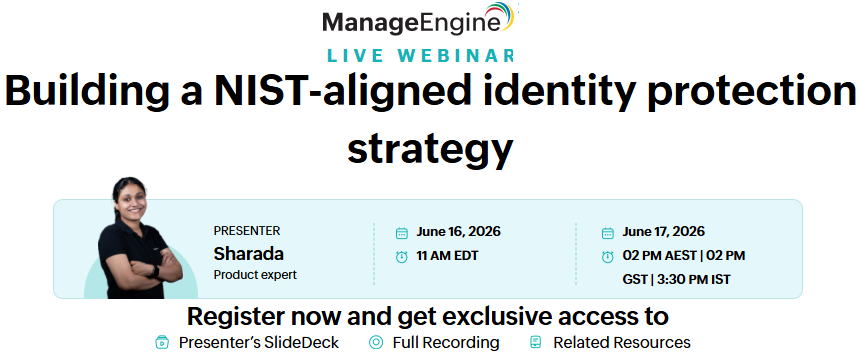
Building a NIST-aligned identity protection strategy
With attackers targeting credentials and regulators referencing NIST guidance more closely than ever, organizations need scalable, standards-aligned identity protection.
Join us for an interactive webinar where we demonstrate how to implement a NIST-aligned identity protection framework that strengthens security without disrupting user productivity.
ffic analytics, firewall optimization, security analytics, and application performance monitoring.
Compliance Meets Cyber Defense:
Making Regulations Work in the Real World
June 24 | 11AM EEST
Join us for an insightful session on how organizations can move beyond checkbox compliance to achieve real cybersecurity resilience. This webinar will explore how regulations like GDPR and NIS2 can be effectively translated into actionable security controls using modern defense strategies. Learn how to bridge the gap between audit requirements and real-time threat detection through continuous monitoring, automation, and enhanced visibility. Walk away with practical insights to build a security posture that is both compliant and truly resilient against today’s evolving cyber threats.
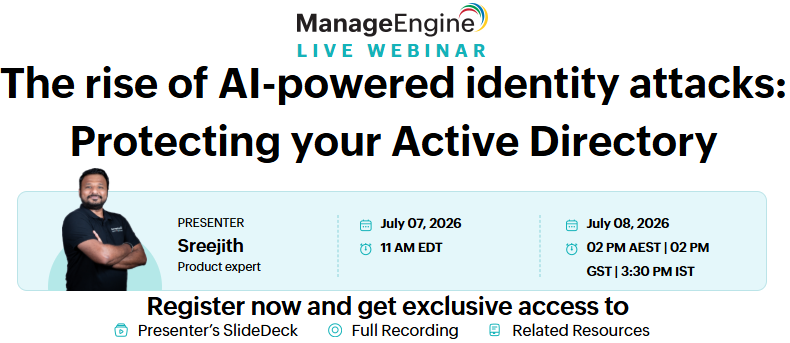
The rise of AI-powered identity attacks: Protecting your Active Directory
July 07, 2026 11AM EDT
AI-powered identity attacks are rapidly emerging as a major threat to Active Directory. Attackers now use automation and machine learning to scale phishing, password spraying, and credential abuse, often bypassing traditional security controls.
Join this webinar to learn how ADSelfService Plus helps organizations protect Active Directory against modern identity attacks while strengthening security, compliance, and user experience across hybrid environments.
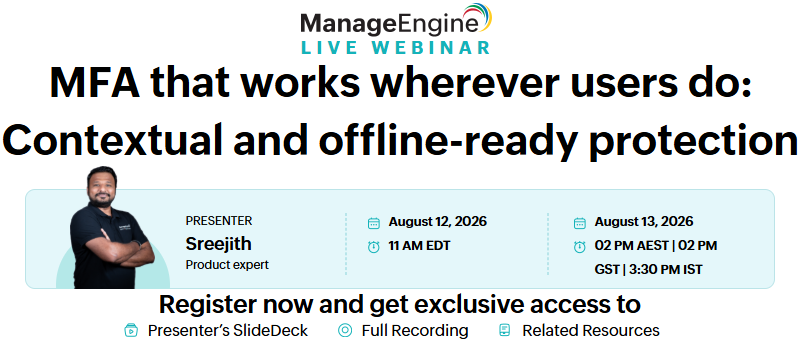
MFA that works wherever users do: Contextual and offline-ready protection
Today’s workforce no longer operates within a fixed perimeter. With remote work, cloud applications, and VPN access becoming the norm, traditional MFA approaches often fall short, especially when users are offline or accessing resources from unfamiliar contexts.
In this webinar, discover how ADSelfService Plus enables modern, resilient MFA that strengthens identity protection without disrupting productivity. Learn how adaptive, context-aware, and offline-ready authentication protects users wherever they work while supporting today’s security and compliance requirements.
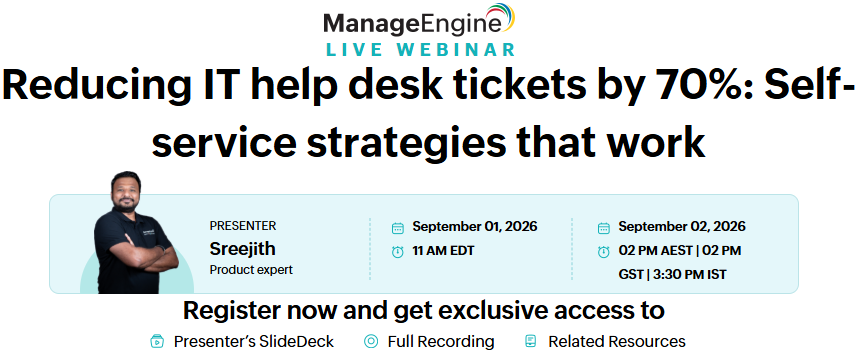
Reducing IT help desk tickets by 70%: Self-service strategies that work
September 01, 2026 11AM EDT
IT help desks spend significant time handling routine identity requests such as password resets, account unlocks, and access issues. As hybrid work expands and user expectations rise, manual support processes increase costs, response times, and user frustration.
Join this webinar to learn how ADSelfService Plus enables secure, user-friendly self-service that reduces help desk workload while maintaining strong identity security, compliance, and service availability.
d compliance requirements.