Servaplex News
The MITRE Corporation & Log360
Learn about The ATT&CK framework developed by the nonprofit MITRE and how it can be used with Log360 for cybersecurity.
Monitoring Wireless Access Networks with OpManager
In this post we'll go over one of the commonly asked questions about OpManager about how to monitor access to wireless networks.
How To See Last Login in Active Directory
In this post we'll go over one of the commonly asked questions about Active Directory about how to see the last login in Active Directory.
Servaplex 2022 Year in Review
Check out the Servaplex 2022 Year in Review where we give you the highlights from the year that was and a glimpse at plans for 2023!
London ManageEngine User Conference 2022 Review
The ME UserConf for 2022 has now been and gone but what a memorable conference it was. It's always great to meet up, network and learn from others in the industry and in that regard the ManageEngine UserConf 22 did just that.
What’s New – October 2022 Patch Tuesday Recap
October Patch Tuesday 2022 was a busy month when it came to patches for some of the biggest names in IT. In this post we'll recap what's new, what you need to know and what you should do to keep your IT systems safe and secure.
How Do You Pick the Best IT Partner For Your Business?
This post will discuss how to choose an IT partner and what to think about to make sure you pick the best IT partner for your business.
Meet, Learn & Celebrate at the ME UserConf – November 14th, 15th
The ME UserConf is back in London. We are delighted to invite you to the ManageEngine UK and Ireland User Conference on the 14th and 15th of November.
IT Ticketing System Software
In this post we’ll give you the info you need to know about IT Ticketing System Software, what it’s used for and the best options available on the market […]
Security for Network Devices – Vulnerability Manager Plus
A crucial component of any IT architecture is network devices, often known as network infrastructure devices. Network devices facilitate connectivity and communication between people, devices, apps and the internet […]
Help Desk Software for Schools
Help Desk software is a tool used to organize, manage and solve various queries or requests raised by customers about day-to-day issues. Whilst using help desk software in schools […]
Managed Service Provider (MSP) Ireland – Is It Right for You?
Do you know what a Managed Service Provider (MSP) is or have you considered using one for your business? In this post we’ll outline the benefits of using an […]
IAM & ManageEngine Seminar Recaps
We’d like to thank everyone who made our two most recent Seminars possible, including all of our attendees, The Royal Marine hotel staff, the team from ManageEngine staff, and […]
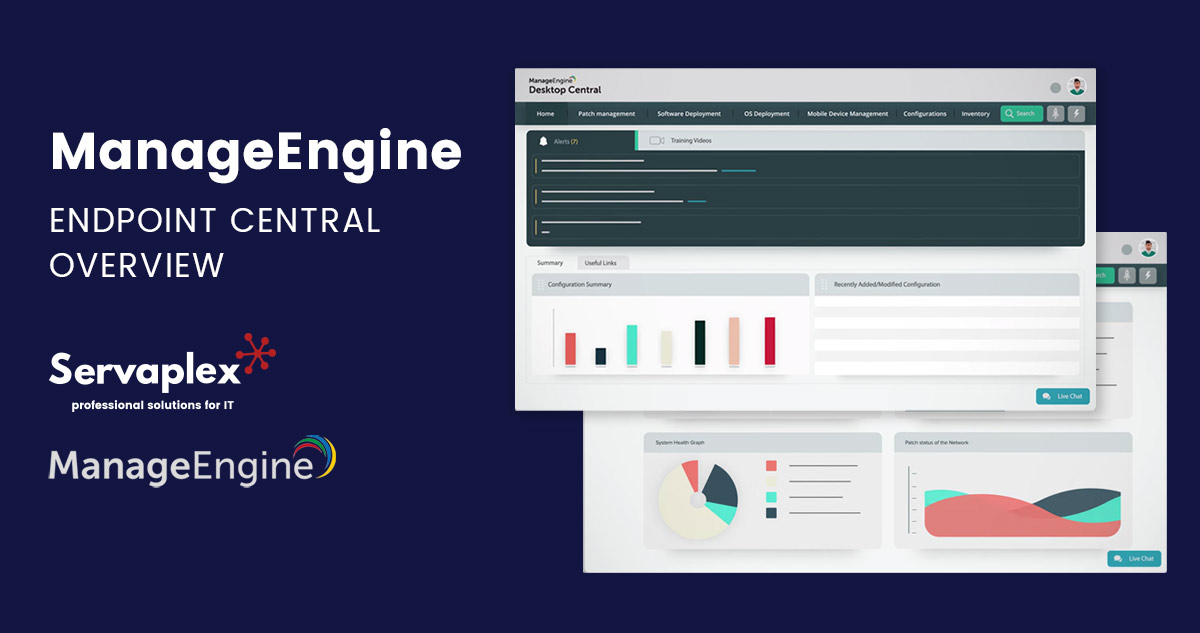
ManageEngine: Endpoint Central Overview
In this post we'll give you the definitive overview to Endpoint Central from ManageEngine so you understand it's features & options.
ManageEngine Endpoint Management & Security Seminar – July 7th
Please join us for ManageEngine's Endpoint Management & Security Seminar in the Royal Marine Hotel, Dun Laoghaire on Thursday July 7th.
Cloud Based IT Asset Management – 2022 Overview for Irish Businesses
In this article we'll give you an overview on Cloud Based IT Asset Management in an Irish context so you learn which are the best options for Irish businesses.